The information technology revolution has brought significant changes to many industries, including manufacturing which depends heavily on industrial control systems (ICS) for monitoring its operations. As a result, ICS has evolved drastically in terms of connectivity.
This has also resulted in the rise of cyberattacks in the manufacturing sector. Let’s understand how we can ensure security for these systems.
What is an industrial control system?
Industrial control systems are an integration of hardware and software to monitor complex manufacturing processes that support critical infrastructure, such as power, transport, wastewater, etc.
Advancement in wireless networking and smart sensor technology has made it desirable to bank upon the benefits of convergence between operational and information technology.
Because these systems are used for critical industries, any downtime in operations can result in significant loss of revenue and brand damage from discontented customers.
In fact, downtime or denial of service (DoS) in critical infrastructure can cause a blockage in the delivery of key services that are essential for people. In extreme cases, this could even result in loss of life.
Use of industrial control systems
- Public infrastructure: This can include gas pipelines, water distribution, and electrical grids.
- Manufacturing automation and control: This covers a wide array of automation in product-manufacturing factories from automobiles to brewing beer.
- Supply chain: ICS and IoT technologies are increasingly being employed to optimize supply chains. Automated warehouses (with robotics) working together with e-commerce systems and rigorous shipping logistics represent the future of supply chain.
Rising cyberattacks on industrial control systems
Industrial controls systems are not immune to cyberattacks and the resulting damage and/or downtime from such attacks.
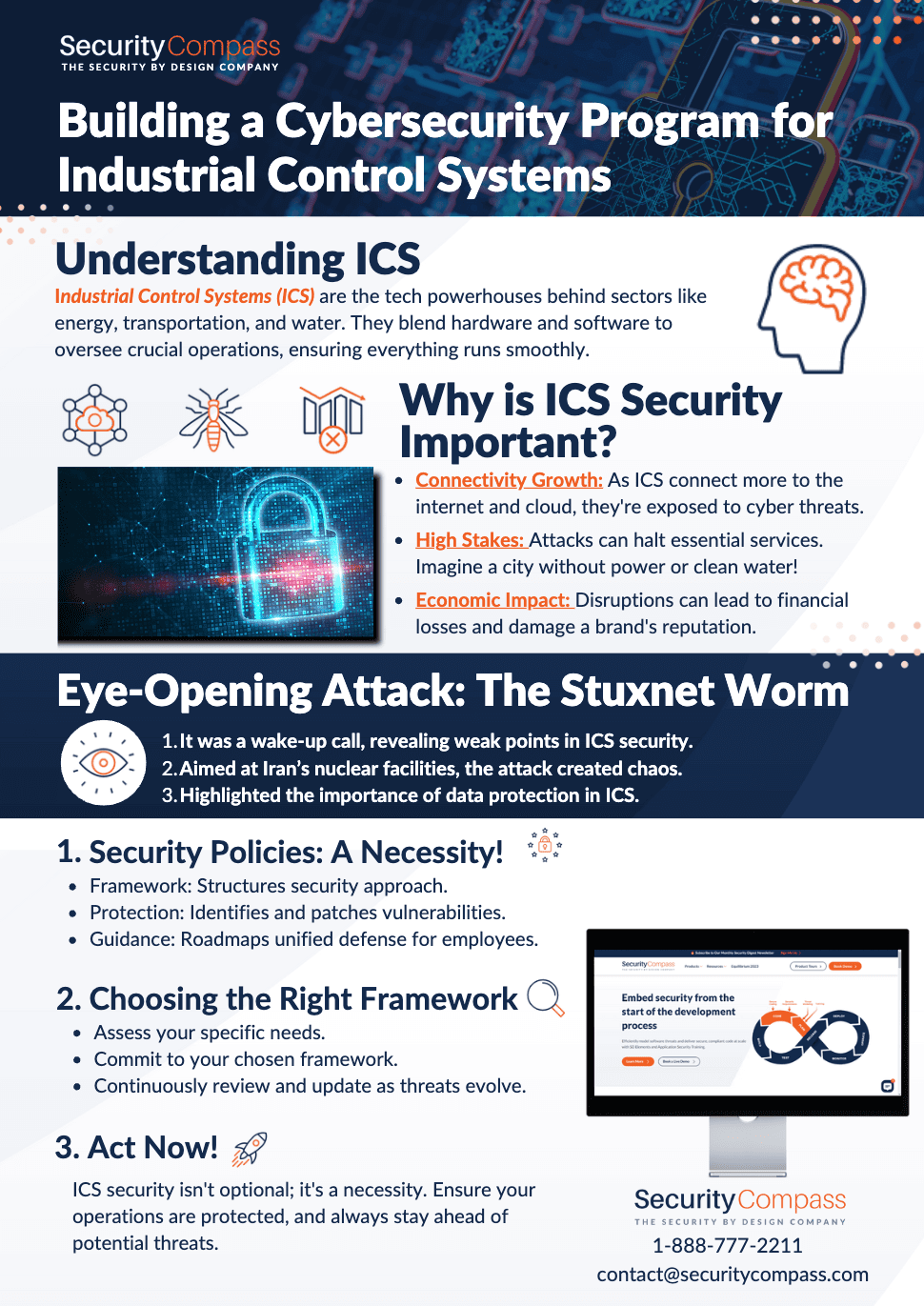
One of the recent attacks that exposed the vulnerability of these systems was the Stuxnet worm used to harm Iran’s nuclear program. In addition to exploiting some Windows 0-day flaws, here’s what all this malware could infiltrate:
- The worm exploited some basic vulnerabilities in the Siemens control system software (including hard-coded passwords).
- Since the attack focused mainly on destroying Iran’s nuclear centrifuges, one component of the malware was designed to tear those apart.
- The malware’s other component gained root access to the programmable logic controllers (PLCs) which allowed it to present the recorded data of normal operating conditions to the operators.
While the operators could see that everything was operating normally, the worm’s impact was throwing the actual behavior of the centrifuges out of tolerance, leading to massive damage before they discovered the cause.
It’s clear, from this example, that protecting data integrity is critical for industrial control systems and that security measures play a key part in accomplishing this goal.
Recent surveys by FireEye and Forrester indicate that these systems are increasingly under attack and that the current state of security in these systems is generally poor.
Increased connectivity broadens the attack vector
More and more, industrial control systems are being connected to the Internet of Things and exchanging data with the cloud. The traditionally-isolated operational technology (OT) networks employed by these systems are increasingly leveraging IP-based networking technologies and connecting to IT networks and the cloud for remote control and monitoring.
System component providers are riding the Industrial IoT wave and supporting many of the IP-based messaging protocols (such as MQTT, XMPP, AMQP, Thread, HyperCat, ZigBee, Pub/Sub) even though they are operating on isolated operational technology networks.
As such, the attack surface broadens and the security implications must be carefully examined.
Security standards for industrial control systems
Since the security of industrial control systems is a rising concern, the International Society of Automation (ISA) has introduced standards to ensure the security of these systems.
Drawing from the insights of experts in industrial automation and control systems (IACS), the ISA developed a series of standards (ISA/IEC 62443) to identify and mitigate security vulnerabilities.
Overview of the ISA/IEC 62443 security standard
ANSI/ISA 62443 is a series of standards, technical reports, and related information, the primary goal of which “is to provide a flexible framework that facilitates addressing current and future vulnerabilities in IACS and applying necessary mitigations in a systematic, defensible manner. It is important to understand that the intention of the ISA‑62443 series is to build extensions to enterprise security that adapt the requirements for business IT systems and combines them with the unique requirements for strong availability needed by IACS.”
The series is organized into four main categories:
- General (62443–1): This group includes elements that address topics common to the entire series.
- Policies and procedures (62443–2): Elements in this group focus on the policies and procedures associated with IACS security.
- System Requirements (62443–3): The elements in the third group address requirements at the system level.
- Component Requirements (62443–4): The fourth and final group includes elements that provide information about the more specific and detailed requirements associated with the development of IACS products.
When it comes to the software development life cycle (SDLC) for industrial control systems, the following parts of the standard define the security requirements in detail:
- ISA-62443–3–3, as part of the series, defines detailed technical requirements for IACS security. There are seven foundational requirement (FR) groups and four security levels (SLs) that are defined in the standard. The required security level for the system is determined through risk analysis. System requirements (SRs) for various security levels are different. SRs are defined in the standard under relevant FRs. Some of the SRs have requirement enhancements (REs) that apply to all or some of the SLs.
- ISA-62443–4–2, as part of the series, defines detailed technical requirements for embedded components, network components, host components, and applications. There are seven foundational requirement (FR) groups and four security levels (SL-Cs) in the standard. The requirements in this standard are derived from ISA-62443–3–3 (system security requirements) but address devices, components, and applications rather than the entire control system.
There’s another alternative framework to ISA 62443 — NIST Special Publication 800–82. This was developed by NIST under the Federal Information Security Modernization Act (FISMA) of 2014.
Overview of the NIST 800–82 standard
NIST Special Publication 800–82 is a guide to ensuring security for industrial control systems. As stated in the SP 800–82 executive summary, it can be considered an ‘overlay’ to SP 800–53:
“The National Institute of Standards and Technology (NIST), in cooperation with the public and private sector ICS community, has developed specific guidance on the application of the security controls in NIST Special Publication (SP) 800–53 Revision 4, Security and Privacy Controls for Federal Information Systems and Organizations [22], to ICS. While many controls in Appendix F of NIST SP 800–53 are applicable to ICS as written, many controls require ICS-specific interpretation and/or augmentation…”
In fact, NIST SP 800–82 refers to many other NIST special publications throughout the document and then goes on to provide the “ICS-specific Recommendations and Guidance” in each case.
There are entire sections dedicated to ICS Security Program Development and Deployment in addition to ICS Security Architecture.
For example, Section 6 of the standard covers the application of security controls to ICS in the context of the NIST RMF (Categorize, Select, Implement, Assess, Authorize, Monitor) and SP 800–53 controls.
Why security policies are essential?
Beyond the actual coding, testing, and deployment of systems and software, there are the policies and procedures related to the control system lifecycle. The lack of a security policy itself can introduce vulnerabilities and predisposing conditions for industrial control systems.
A comprehensive and documented security policy is necessary to define the roles, implementation guides, and enforcement of the system’s security program. Management support and governance of the security policies and procedures is a key driver in the success of any security program.
Both ISA/IEC 62443 and NIST SP 800–82 cover the topic of policies and procedures in-depth, but each takes slightly different approaches.
The 62443–2 category is dedicated to this topic and is broken up into four subparts that all speak mostly in terms of building a cybersecurity management system that is relevant for IACS environments.
This is also referred to in the standard as an IACS security program or (more frequently) an IACS security management system.
- The first part (62443–2–1) outlines requirements for a successful IACS security management system, while part 2 (62443–2–2) provides guidance for implementing such a system.
- The third part (62443–2–3) goes into detail about the recommended patch and change management processes for the system, while the fourth part (62443–2–4) echoes security program requirements, but this time for IACS service providers.
NIST SP 800–82 is also an excellent resource for policies and procedures and even dedicates an entire section in Appendix C about identifying vulnerabilities and predisposing conditions related to (lack of) policies and procedures.
Appendix G covers the list of recommended controls and, in essence, recommends to have documented security policies and procedures for each control family (an overlay of SP 800–53) in the standard.
Which ICS security framework is right for you?
Both the ISA/IEC 62443 and NIST SP 800–82 standards are comprehensive in their coverage and guidance for ICS security.
Although there are other security standards, initiatives, and recommended practices in this space, these two frameworks are the most well-known and adopted.
Since connected systems are always prone to new threats, a multi-faceted approach is required to address the varying threats. Following a security framework can help guide organizations into such a holistic approach.
In many cases, the selection of a framework will depend on the industry and associated regulatory drivers that may call for a specific framework. The public sector, for example, is generally required to follow the NIST standards.
The main thing is to select and execute on one of the standards because to do nothing is a recipe for disaster. Whatever framework you choose, it is good to be familiar with both , as each framework provides a wealth of information about protecting industrial control systems.