Author: Pranoy De, Solutions Engineer at Security Compass
In the last couple of years, we have witnessed large data breaches, including Marriott, Equifax, and Facebook, making cybersecurity an important talking point in and around the tech industry.
The Problem
Most developers are not security experts, and their ability to mitigate vulnerabilities effectively, efficiently, and comprehensively has to be questioned.
A survey found that more than 50% of companies rated their developers’ knowledge about security as poor or below average.
– Security Compass, 2017. “Managing Application Security Survey”
Furthermore, security language is very different than developer language. An example security requirement can look something like this :
‘Implement server to server authentication’. With the solution hint being something like:
- A presentation-tier server may need to authenticate a middle-tier server and vice-versa.
- Server-to-server authentication is commonly done using X509 certificate mutual authentication
A developer reading this can understandably find it very difficult to translate such abstract information into a tangible coding solution.
How big is the task at hand?
Developers may have to defend against attacks that are application-based (e.g., malware, computer virus, SQL injection, cross-site scripting, etc.) or network-based (e.g., DoS attacks, network hacking, botnets, etc.).
Thankfully, developers are not expected to provide physical protection by standing guard outside the building, but who can predict the future!
Given all that we expect from developers, here is what a sample job description would look like:
‘Seeking a smart, hardworking, self-starter with good communication skills and a minimum of 8 years of experience. The role requires writing code aligning with our business needs, testing the code, deploying the product and providing support to any customers that are having difficulties. Additionally, the code would need to be secure and compliant with the latest security standards in the industry while continuing to work in a fast paced and agile manner.’
This might seem like too much to ask for. Instead, let’s ask ourselves what we can do to help developers perform these tasks while being comprehensive in the defenses and working in a fast-paced agile environment.
The ‘Dev’ in DevSecOps
DevSecOps has been a trending buzzword lately. Small and large organizations have finally shown an interest in maturing their security processes and programs.
A good DevSecOps pipeline focuses on improving:
- Communication between concerned teams (Business, Risk, Compliance, Security, Development, Operations, etc.)
- Security awareness and training among developers
- General mindset around security (incorporating it as part of the process as opposed to an afterthought)
Going back to our previous example of an authentication-based security requirement, imagine this requirement included a developer training module, code snippets, and additional tips and tricks on how to begin approaching this task. A developer would instantly be much better positioned to implement the aforementioned security requirement.
The key takeaway for developers here is that the security-related tasks which finally make their way to the dev board will be well-groomed and scoped out, thus minimizing any ambiguity in its implementation, testing, and deployment. There will also be a focus on tying the progress made by developers all the way back to the Risk, Compliance, and Security teams so that the overall progress can be tracked and measured by all stakeholders.
This mindset is becoming increasingly popular as the industry continues to realize that security cannot be the responsibility of a single department anymore and that the approach needs to be more holistic.
Where do we start?
Our initial problem statement identified developers not being security experts. A good starting point for addressing this issue can be based on the principles of DevSecOps. The technical expertise required to execute security tasks effectively may already exist within an organization. The problem is that this knowledge is spread across different teams. To best leverage this knowledge, we would need a platform/service/tool that can perform the necessary translations so that the generated security requirements (which are very abstract) can be converted into well-groomed dev stories, making it clear to the developers exactly what is required to be done.
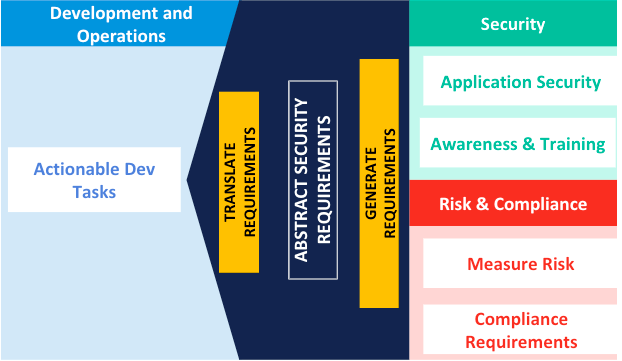
To be more specific, the aforementioned platform would:
- Generate security requirements while acting as a threat modeling tool.
- Translate these requirements into well-defined developer tasks based on the relevance of the tech stack and system architecture in place.
- Associate each task with the required security training that would help in fully understanding the threat as well as gaining valuable insights on how to mitigate against it.
- Sync seamlessly with the ALM (Application Lifecycle Management) tool like JIRA, Rally or PivotalTracker, thus preventing developers from having to worry about using ‘yet another tool’.
What have we gained?
With a mature DevSecOps pipeline, implementing the correct processes, developers can be confident about the security tasks they implement and, more importantly, no longer need to make security an afterthought. Security (which has traditionally been a waterfall process) can now, with the help of these tools and processes, be integrated as part of an agile feedback loop, allowing us to continuously improve without slowing down. If we get this right, being a developer today won’t be so daunting!
To learn more about the Security Compass Solution, contact us here.

