So You Don’t Have To
Application vulnerabilities and risks multiply faster than the speed of ordinary business security. Fortunately, companies can rely on Security Compass and SD Elements to give them a head start toward conquering risks while maintaining usability.
In our recent release of SD Elements, SDE4, we continue to build our reputation for providing extraordinary business security solutions with deep content that we deliver at lightning speed. We recently sat down with our Lead Application Security Researcher, Farbod Foomany, to talk about his background, work, and team.
“One of the greatest things about what I do is that I get to work on something different each day. Anything someone discovered for the first time is exciting for me and most people in this field. When a vulnerability is found in something that is commonly used, it is interesting. With my background, any crypto algorithm vulnerabilities and SSL vulnerabilities are also interesting, both the cause and the consequences. Mostly, the quest for our clients satisfies my curiosity and need for innovation, that not only gives me a sense of accomplishment, but helps our clients be able to rely on our research as well.”
— Farbod Foomany
During the 80’s, a time when researchers were puzzling over the vulnerabilities that allowed some of the first self-perpetuating computer viruses like Elk Cloner and Brain to spread via floppy disk, Farbod’s interest in computer science started. His father brought a Commodore computer home, and he learned that he could use words to code and have the computer draw shapes. Farbod continued to discover what he could accomplish with code during the late 80’s when the ARPANET had already morphed into the internet, a 500 network system sponsored mainly by governments and computer science researchers. Jack L. Brock, Jr., Director of Government Information and Financial Management Issues testified about internet vulnerabilities before the US Congress. He described what the internet was and that vulnerabilities in the networks allowed a virus to cause “an unclassified multi-network system connecting over 60,000 computers nationwide and overseas — to shut down.” A matching report filed by the GAO (Government Accountability Office) described the impact of the DNS attack and the virus that caused it; “…it was the first to use networks to spread, on its own, to vulnerable computer systems.” This was the vulnerability landscape that existed when Farbod’s fascination with code turned from fun into serious science, and he started writing algorithms through high school and into college.
The risk and vulnerability landscape continued to change and shift through the 1990’s. At the end of the decade Farbod was completing his bachelor’s degree in Electrical Engineering, and when he received his degree in 2000, ICISC was already hosting its third annual conference in Seoul, Korea. The papers and presentations provide a microcosm of the concerns foremost on the mind of InfoSec researchers of the time. One group of researchers explained the need for integrated tools, “So far there is no formal and standardized technology for Security Evaluation System, and vulnerability assessment tools developed by individual software companies are used for security evaluation of the network instead…it is hard to get integrated security evaluation report from the vulnerabilities found by each tool.” Other researchers in the burgeoning field of InfoSec were focused on cryptography, and soon, Farbod joined their ranks.
Even though Farbod’s degree was in Electrical Engineering, he still had a deep background manipulating code and mathematics. So, when he finished his degree, he worked as a programmer. He was in a company that worked on Java smart cards in financial applications. Farbod developed a lot of code related to encryption and security algorithms. This was his intro to the InfoSec world and vulnerability landscape, and he found that he could utilize his mathematical skills and knowledge:
“I really love mathematics and like cryptography, and because of my undergraduate degree in electrical engineering, I could, and still can, go one level beyond how an algorithm can be attacked. It also helps when researching the IoT; the way the devices communicate is in the end through the wireless and physical layer. I can understand the process, vulnerabilities and weaknesses on a deeper level, because I am familiar with the concepts of electrical engineering and Control Systems.”
Farbod eventually became part of another security group since he had experience writing crypto algorithms. His fascination and knowledge continued to grow, and Farbod decided to learn what was happening inside the computer, the electrical concepts. Eventually he realized that he was more interested in computing, and pursued a master’s degree in this discipline. The threat and risk landscape also continued to evolve. Researchers were studying vulnerabilities and exploits like the buffer overflows in QuickTime and eZnet, and OWASP came out with its first Top 10.
During the 2000’s, the threat landscape broadened with exploits that took advantage of a range of vulnerabilities like SQL injection vulns and DNS exploits performed by nation-states like W32. Dozer. In this landscape, Farbod continued to deeply enjoy his InfoSec work, and he continued to work with crypto algorithms and banking applications. He also started to work on voice recognition and physical biometrics for banking apps, and he went back to college and received his doctorate in biometrics and philosophy, which is an overlap of InfoSec and his previous work as a programmer.
After his PhD, Farbod spent 3 years in another academic setting at Ryerson University. He worked on signal processing research and learned a lot about how to manage a research team and how to collaborate with other resourceful researchers. Throughout his time at Ryerson, Farbod kept a close eye on the InfoSec field, and he noticed that exploits were getting more sophisticated and that more and more devices and applications were accessible. Looking at the trends of the past he noticed the increasing potential for harm. He saw an especially nasty 2011 spear-phishing exploit that could have been avoided with better Access Controls, and during this time, his main interest began to shift away from individual applications; he began to wonder how we can manage data security in the design phase. How does one design guidelines to make a system secure? How does a developer develop their own baseline knowledge of InfoSec to code securely in the rapidly shifting vulnerability landscape? He wanted to understand how developers can include all the guidelines in the design of a system and make sure all the requirements are met.
In 2013 just when OWASP was coming out with their most recent Top 10 list, Farbod found an opportunity with Security Compass that looked fascinating. It would allow him to deepen his research on application security and answer the questions formulating in his mind. He joined the company as an Application Researcher for our SD Elements Content Research Team.
When Farbod studied in academic settings, he spent one to three years on the same topic, and he was concerned that he would be unable to research the vulnerability and compliance landscapes with the agility and pace required for a field that changes at colossal speeds. This one concern was quickly alleviated. Working with his team at Security Compass, he was able to adjust directions and not waste time. He finds the fast pace, creative problem solving, research, and writing satisfying and fulfilling.
That is true of the majority of our content research team. Everyone is accomplished in their own way with each team member arriving at Security Compass from different paths. Everyone on the team has at least a master’s degree related to security and have all worked on security research. They have published papers, and everyone shares the same background with degrees in computer science and specializations in security. The team keeps current on the vulnerability landscape through research. They write about their discoveries and pass that onto our clients through SD Elements updates, conference presentations and papers. In general, the team is active in InfoSec, and they recently published a paper in ISACA and gave a talk at OWASP AppSec USA in October 2016.
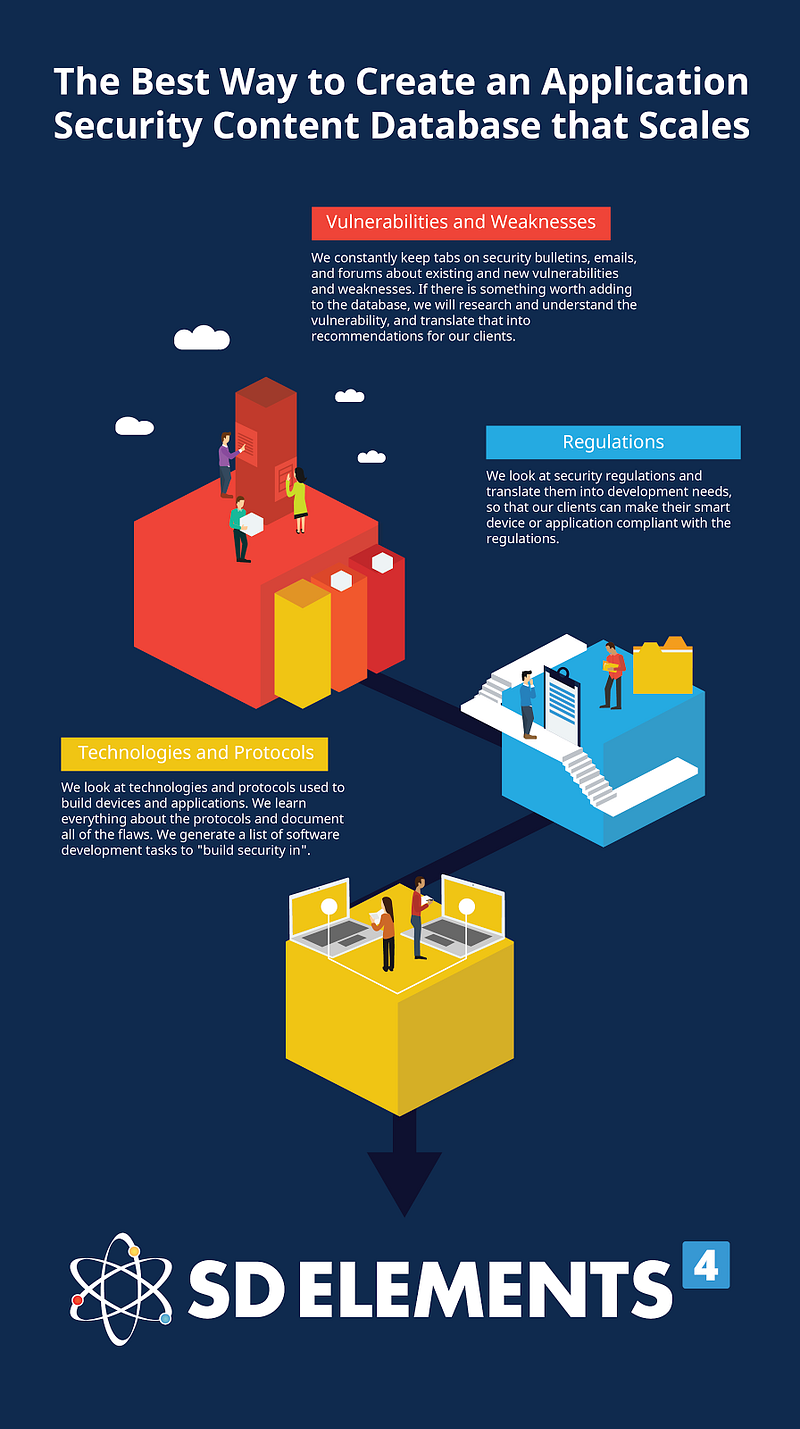
The team works under the premise that “There is nothing else that impacts our clients as much as content research,” and their ultimate goal is to:
“Deliver content so our clients can worry less when they follow the guidelines we research and include with SD Elements 4. We want our clients to develop secure applications, and they shouldn’t have to go and do their own research other than getting a deeper understanding of what our content team writes. We want them to follow simple guidelines to have a secure system. In a centralized way, we research for them.”
Farbod and his team keeps tabs on regulations, exploits, and the vulnerability landscape. They pass that information to our clients through the ever-current SDE4. Our clients stay steps ahead of the shifting Information Security landscape, eliminate vulnerabilities and create secure software before scanning even begins. Farbod put it this way:
“The main point is that nothing is overlooked. They don’t have to have their own security team due to our thoroughness.”
Security is elaborate and continuously changing and covering up security problems is not a solution. If you want to enjoy the benefits of Farbod and his team’s deep experience and easily integrate the most current security research into your application development, then you can go to the main product page to learn more about SD Elements 4. While there, you can sign up for a free demonstration.

